Modern Workforce Authentication
Total access.
Zero friction.
Zero Trust security.
Accelerated productivity.
Proximia delivers both.
Flexible Login Options
Your way, phones optional
Silent Second Factor
Presence-based, no codes
Persistent Protection
Beyond login, continuous
Remote-Ready
Secure access anywhere
Built to Integrate
Works with your stack
Boost Productivity
Save everyone time
18x Faster. Because Time Is Money.
Passwords are expensive. They create user friction, overload IT teams, and remain the #1 cause of security breaches.
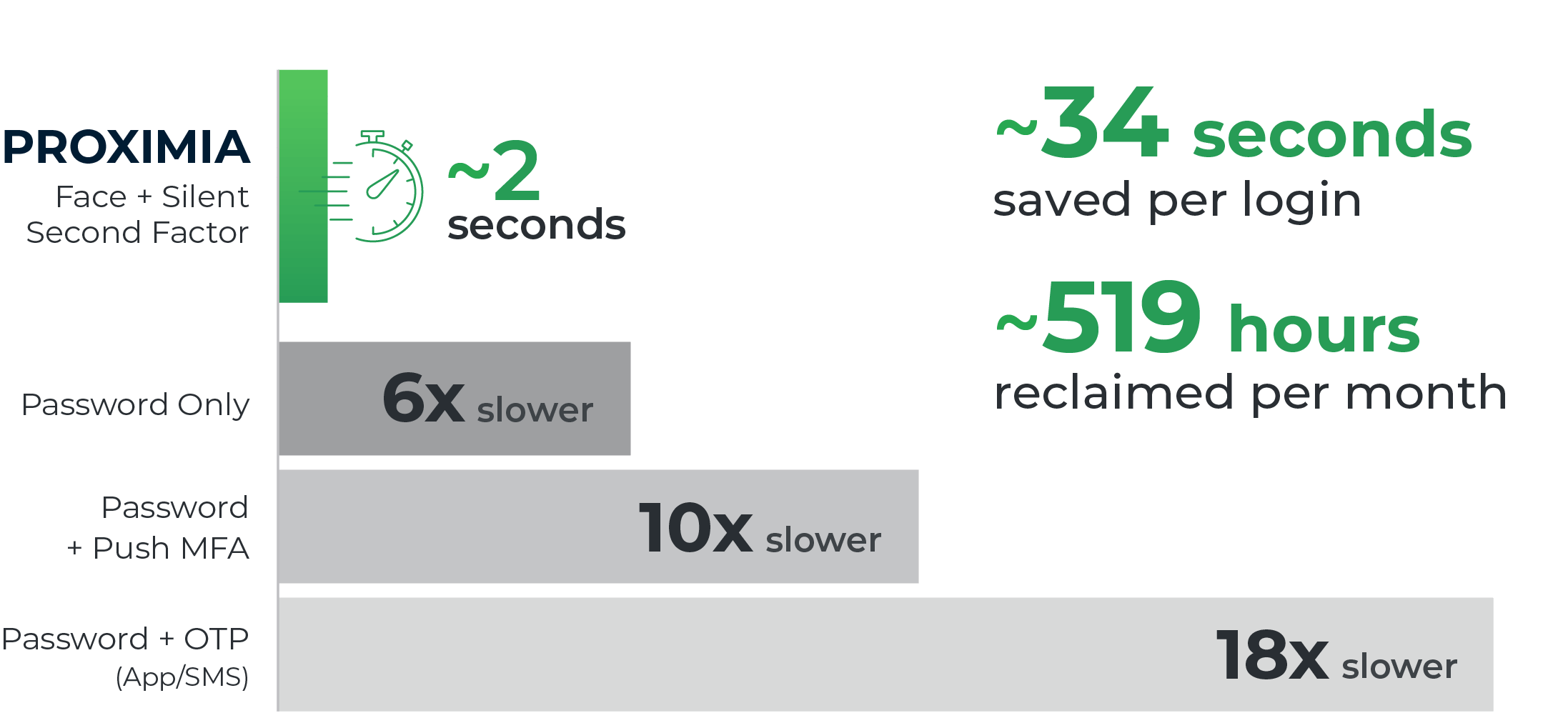
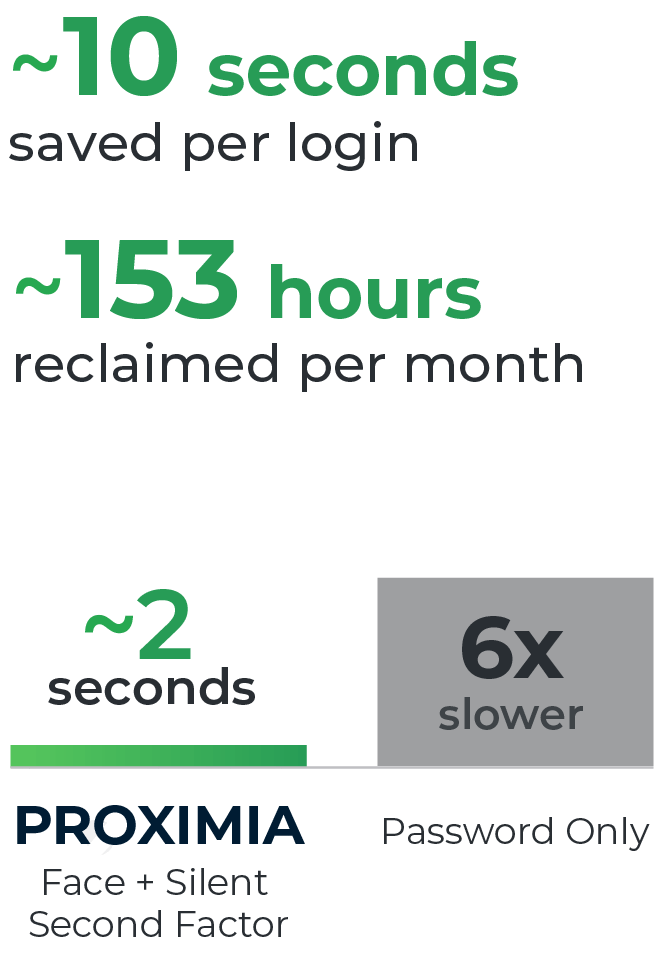


Estimates based on 250 users, 10 logins per day / per user, 22 business days per month.
Increase Productivity
Every login = ~30–90 seconds of cognitive recovery time, costing productivity.
Eliminate Tickets
~660 hours per month lost to users and IT for password resets and MFA lockout handling
Reduce Noise
~150-300 hours per month spent by IT reviewing false alerts and suspicious logins



Credential-Based Attacks
Eliminate the #1 source of breaches at the root.

Post-Login Exploits
Close the post-login security gap every other IAM leaves open.

Insider & Physical Threats
Stop unauthorized access by requiring physical presence.
Would one platform make IT simpler?
Your workforce needs security that fits existing systems, not the other way around. Proximia integrates with your stack — without forcing change.
Get up and Running Fast
You don't have time for long rollouts. With Proximia, deployment is fast, lightweight, and designed to give your business immediate value.

What could Proximia do for your business?
Eliminate friction with seamless access
Give all employees a quick, secure login experience — without passwords, lockouts, or extra steps.

Provide unmatched protection, reduce risk
Keep every session secure from start to finish with live proximity and persistent authentication. Security is continuous, not static.
Simplify IT with one highly integrable solution
Reduce overhead, cut down resets, and manage users, devices, and policies from a single pane of glass. Reduce your IT burden.
Take control of your digital security today
In a world where cyber threats are constant, so should be your protection.