Every time authentication gets stronger, it tends to get more complicated.
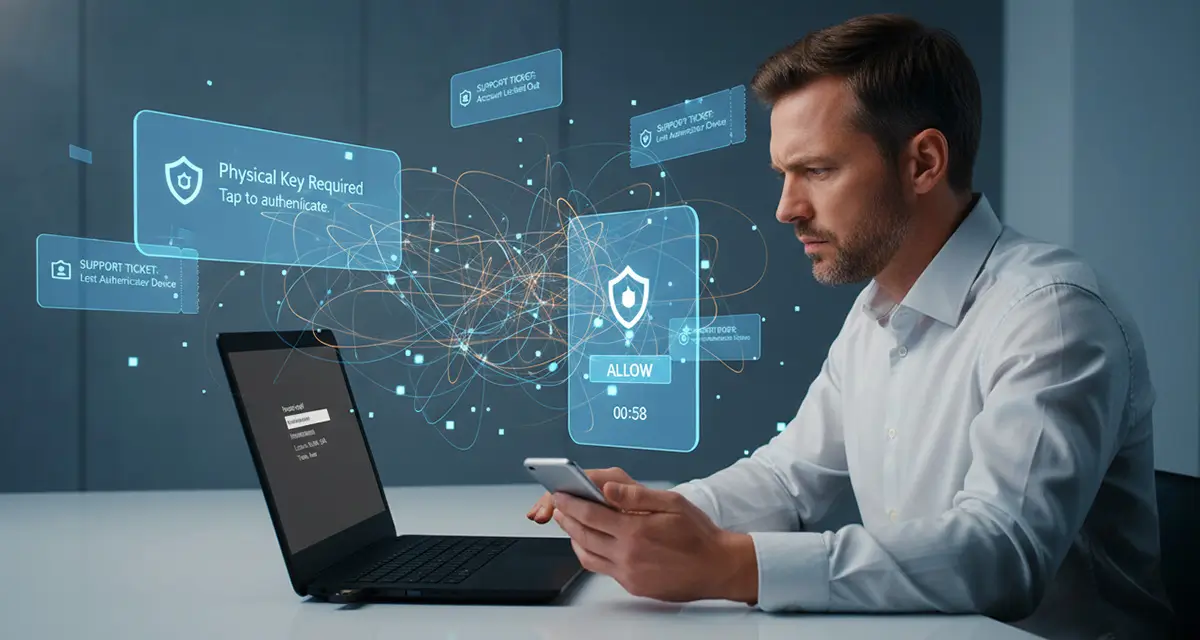
Most MFA and passwordless tools still rely on multiple authenticators: phone apps, biometrics tied to personal devices, security keys, backup codes, and passwords as fallbacks. Each workflow or application may require its own setup. Each new device requires re-enrollment. Each lost or broken authenticator triggers a recovery process.
This phenomenon — authenticator sprawl — is one of the biggest drivers of help-desk volume today. And it’s not a user problem. It’s a design problem.
Conventional authentication systems are built around the assumption that login is the center of trust. So every device and application gets its own method for proving identity. Users move between a laptop, a browser, a mobile device, a VPN session, a remote desktop — and in each context, they may need a different factor. When something breaks or doesn’t behave as expected, they call IT.
This creates an operational burden that grows as environments become more diverse. Organizations invest in stronger authentication, only to find themselves managing an ever-increasing array of factors and recovery processes.
A better approach simplifies identity instead of multiplying it.
A model based on continuous, presence-aware authentication uses a small number of trusted, bio-linked devices to validate users throughout their session. Instead of relying on a different factor for every workflow, authentication becomes unified. Instead of re-enrolling every time hardware changes, identity anchors to presence rather than device-specific credentials. Instead of repeatedly prompting users, trust persists as long as the right person is present.
The impact is dramatic:
- Fewer login events
- Fewer MFA prompts
- Fewer recovery tickets
- Less user confusion
- Consistent security across modern and legacy systems
For IT teams, this means fewer breakpoints and a more predictable set of workflows to support. For users, it means authentication becomes nearly invisible.
Strengthening authentication shouldn’t require expanding the number of authenticators people must juggle. It should make identity simpler, more consistent, and more resilient.
Continuous, presence-driven authentication achieves that — delivering stronger security without the operational overload that traditional passwordless approaches inevitably create.